Protect Your Data
All engagements begin with a
complimentary 15-minute consultation.
Signal Messenger
End-to-end encrypted. No metadata retention. This is how to reach me.
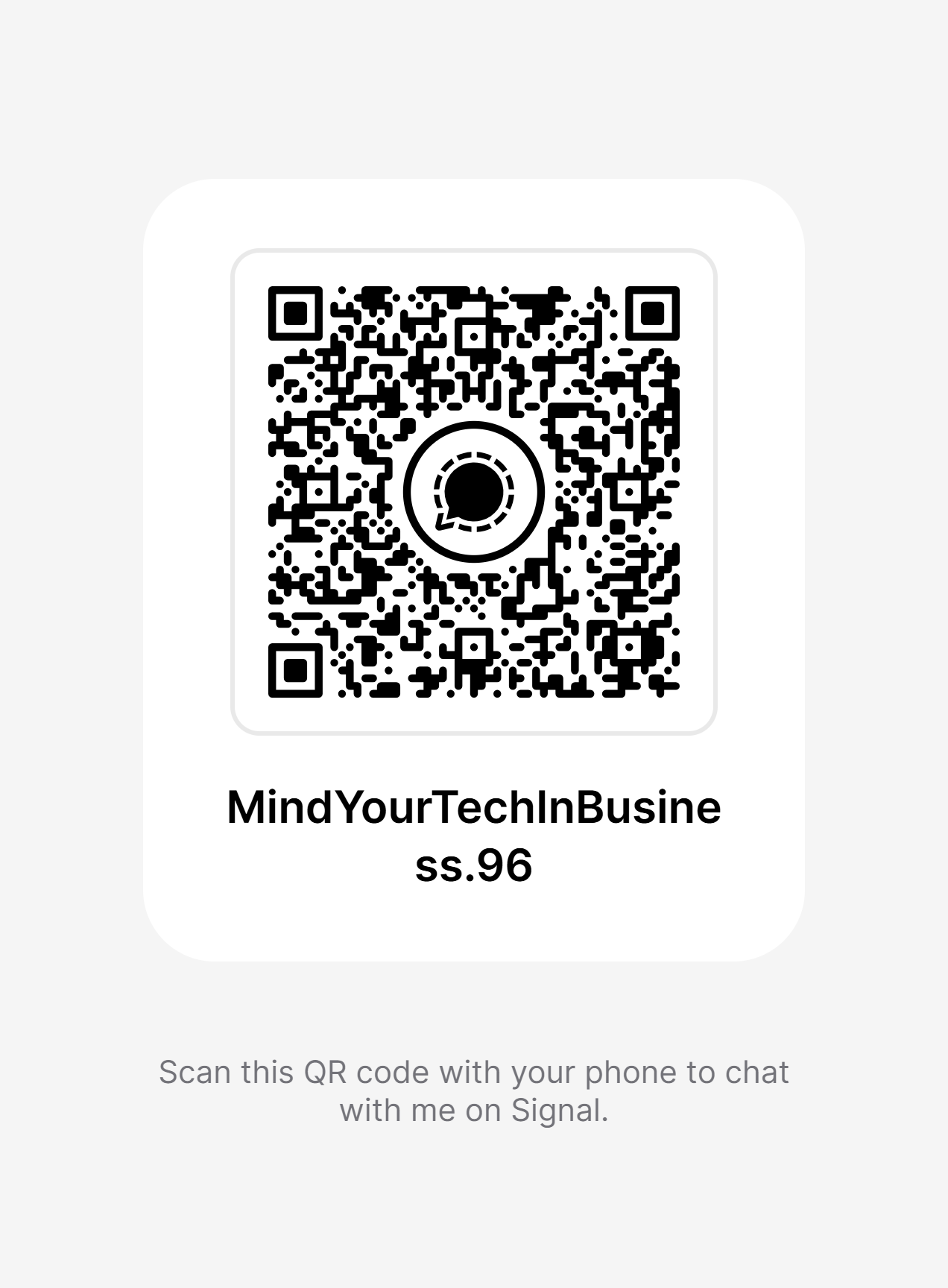
Signal QR Code
1. Install Signal | 2. Scan QR or add username | 3. Send encrypted message
Mission-Specific Templates
Founded by a Veteran & Community Organizer,
turned Sovereignty Protector.
I understand mission-driven work because I've done it.
Your protection is my purpose.
Subscribe & Follow
Substack: Articles, investigations, and live demo announcements.
GitHub: Open-source tools, scripts, and findings.